Author: Stacey Yoakum
While the long-term care sector has been battling staffing shortages, low census numbers, and the clinically complex challenges of COVID-19, healthcare has reported more data breaches than any other sector in 2021. You might be left asking, what makes healthcare data so valuable?
Medical records are worth 10-40 times more than your credit card if sold on the black market. You can easily cancel a credit card if it is stolen, and your social security number cannot, which allows cybercriminals to open credit cards and loans, file false tax returns, purchase prescriptions, and make false medical claims.
Let’s start with the easiest yet very effective way to protect yourself against phishing attacks which could cost you millions of dollars in fines.
Phishing is one delivery mechanism for ransomware and other malware. Some examples of common phishing attacks include:
- Malware infects a machine by tricking users into clicking on a nefarious attachment included in a phishing scam. An analysis of more than 55 million emails reveals that 1 in every 99 emails is a phishing attack, and the ability to recognize the real from the fake is becoming increasingly difficult.
- Spear Phishing is a targeted phishing email attack aimed at a specific user that relies on data previously collected about the user. Once they have gathered information, criminals send urgent emails to entice recipients to act immediately on their requests.
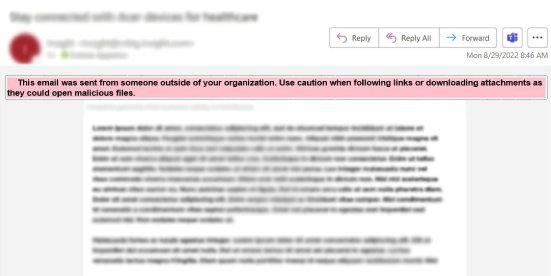
- Whaling is a type of spear-phishing attack that is more focused on high-profile targets. This tactic uses the target’s name and asks the recipient to transfer funds, purchase gift cards, manipulate payroll, and even install applications on their computer. The banner in the box below, or a similar message, alerts your organization’s users that the email is an imposter and to not act on any requests in the email.
- Link Manipulation leads users to an infected website, and malware is downloaded and installed without the user’s knowledge. The link might also lead users to a malicious website and trick users into providing sensitive information such as their password, date of birth, social security number, and/or financial and personal information.
If you fall for phishing attacks, consider installing anti-malware on your computer or device.
In 2020 alone, Think Anew prevented millions of attempted network breaches, blocked millions of spam and malicious emails, and hundreds of thousands of phishing attacks.
Ensure you have the message below, or a similar banner note, included in any email received from an external sender.
This email was sent from someone outside of your organization. Use caution when following links or downloading attachments as they could open malicious files.
What is Ransomware and How Does it Work?
Ransomware (i.e., ransom malware) is a form of malware designed for the sole purpose of extorting money from its victims. In healthcare, ransomware
is considered a data breach for reporting purposes.
Ransomware can lock your computers and encrypt data and essential system files on infected computers and other connected devices. Cybercriminals will then extort you for money to recover your files, affecting access to your medical records and email, among other business-critical applications.
So, how can you best protect yourself from ransomware? It is critical that you work with your IT partner on an educational phishing campaign promoting cyber security awareness.
Ensure Your Educational Phishing Campaign Covers the Following Safe Computing Tips:
- Never click on unsafe links. Train users on the types of phishing attacks and the consequences of malware and ransomware. Always avoid clicking on links in spam messages or on unknown websites.
- Do not open suspicious email attachments. Avoid opening any dubious-looking attachments. To ensure the email is trustworthy, pay close attention to the sender and check that the address is correct. Never open attachments that prompt you to “install” to view them.
- Avoid disclosing personal information. Never reply if you receive a call, text message, or email from an untrusted source requesting personal information; that is a spear attack. If there is any doubt about the legitimacy of the email, contact the sender directly.
Use a Security Banner
Have your IT provider include a security banner on all external senders’ emails. Whaling is on the rise. You must train users that regardless of the name in the “From” field, if the email appears to come from someone from within the organization but the banner is present, it is a phishing scam. They should immediately delete and report it to their security officer.
Never Use Unknown USB Storage Devices
Never connect a USB or other storage media to your computer if you do not know where it originated. Cybercriminals may have infected the storage medium with malware or ransomware, then placed it in a public setting to entice someone to use it. Research consistently shows that close to 50% of devices within controlled tests have been accessed to view the content.
Keep Your Network Safe From Connected Devices and Programs.
- Keep systems up to date. You must regularly update programs, and operating systems and apply security patches to help protect you from malware. Keeping your systems up to date makes it harder for cyber criminals to exploit vulnerabilities in your programs.
- Keep tablets protected. A quick search of Google will show you that you can find plenty of archived application templates to secure a COVID-19 telehealth device, but virtually no information on the requirements to keep these devices HIPAA compliant. There has been $200 million awarded for these COVID-19 devices. At an average of $1,000 per device, that means approximately 2 million additional devices are floating around our communities with the potential of having inadequate mobile device management installed.
- Ensure all mobile devices have the proper mobile device management software installed.
- Educate remote workers. Remote work during COVID-19 increased the average cost of a data breach in the United States by $137,000. Therefore, it is crucial that you work with your IT provider and create a solid Computer Usage Agreement to educate your users on the requirements of working from home. For example, make sure the audio and video conferencing tools your employees are using are HIPAA compliant.
Make sure you are properly backing up your data.
If all other defenses fail, a resilient backup plan for all critical business applications is your best defense against ransomware. Backups should be replicated over different geographic locations, require PIN authentication, and utilize notification alerts whenever suspicious
activity occurs.
Use a network monitoring tool.
If you are using a proper network monitoring tool, you’ll know the instant a hacker tries to break into your system and thus be able to prevent it. Unfortunately, not all monitoring tools are automated, so you must utilize additional tactics. For example, phishing simulations allow you to create fake phishing attacks to monitor employee knowledge and identify who is at risk for a
cyber-attack.
Education is Key!
Train often and educate your users on current threats by using real-life examples when possible to make the emails relatable. Also, use a security banner and train how to identify whaling emails. Keep your systems up to date, and work with your IT partner to ensure they use cloud-based backups that are replicated and secure.
If you need assistance with an IT risk audit, contact us at [email protected], and we will happily assist! We’re there when you need I.T.®.
Data Breaches by the Numbers:
- Confirmed data breaches in the healthcare sector increased by 58% this year (Verizon)
- The global average cost of a data breach is $3.86 million (IBM)
- The average cost of a healthcare breach is $9.42 million (HIPAA Journal)
- The healthcare sector spends the most time in the data breach lifecycle at 329 days (IBM).
- A breach lifecycle of fewer than 200 days costs $1 million less than a lifecycle of more than 200 days (IBM).
- 23% of data breaches are the result of human error (IBM).